Beyond the Perimeter: Why Zero Trust is the Only Viable Defense
The Castle is Empty, The Walls are Gone
For decades, the fundamental concept of cybersecurity was the "Castle and Moat" strategy. You build a massive, heavily fortified wall around your corporate network. Anyone on the outside is a potential threat; anyone on the inside is trusted.
But over the last five years, enterprise architecture has radically transformed. We moved our databases to the cloud. We decoupled our frontends. Our employees started logging in from coffee shops halfway across the world.
The perimeter hasn't just expanded; it has completely evaporated. If there is no "inside" the network anymore, how do you secure it?
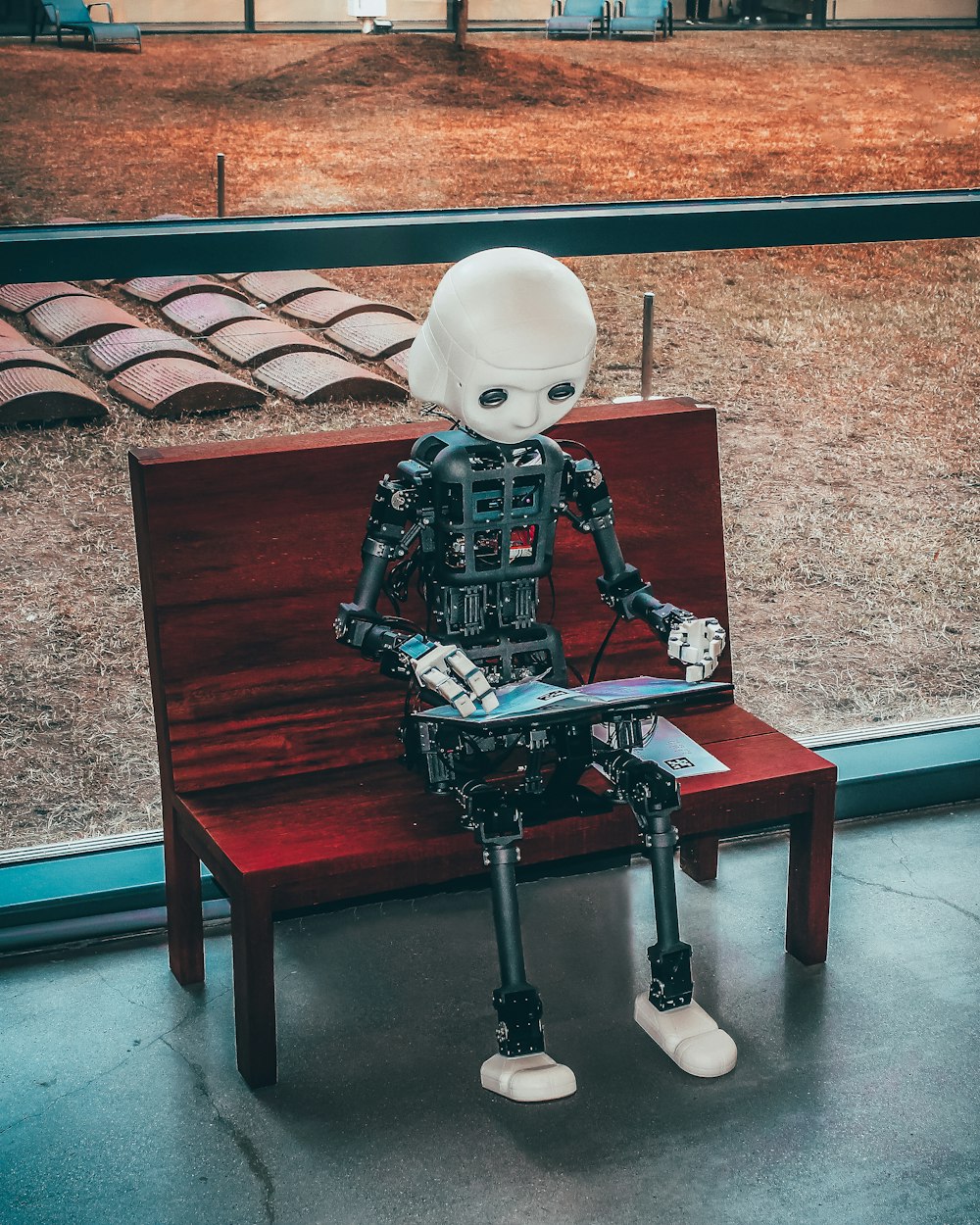
Enter Zero Trust Architecture
Zero Trust is not a specific software you buy; it is a fundamental shift in engineering philosophy. Its core tenet is ruthlessly simple: Never trust, always verify.
In a Zero Trust network, simply having the correct password or being on the company VPN grants you absolutely zero inherent privileges. Instead, access is granted based on continuous, dynamic verification.
The Three Pillars of Modern Defense
To build a resilient cyber strategy today, organizations must implement three core concepts:
- Explicit Verification: Systems must authenticate every single request. They analyze the user's identity, the device's security posture (Is the OS updated? Is antivirus running?), and the geographic location of the login attempt.
- Least-Privilege Access: If a marketing executive logs in, they should only have access to the exact marketing tools they need. They should not have lateral access to the HR database or the engineering servers.
- Assume Breach: This is the most critical psychological shift. You must architect your systems under the assumption that a hacker is already inside your network.
By micro-segmenting applications and demanding continuous authentication, we don't just stop hackers from getting in; we stop them from moving around once they do.




0 Comments
Loading comments...
Leave a Reply